Introduction
In today’s rapidly evolving digital landscape, organisations face a critical paradox: whilst legacy systems continue to power essential business operations, they simultaneously represent some of the most significant security vulnerabilities in modern IT infrastructure. These older systems, often built decades ago, were designed in an era when cybersecurity threats looked vastly different from today’s sophisticated attack vectors. Yet, they remain deeply embedded in the operational fabric of countless organisations, from financial institutions to healthcare providers, manufacturing facilities to government agencies.
The challenge is clear: organisations cannot simply abandon systems that have proven reliable over years or decades, especially when they support critical business functions. However, maintaining these systems without addressing their security vulnerabilities is no longer an acceptable option. The cost of a breach, both in financial terms and reputational damage, can be catastrophic.
Understanding the Legacy System Landscape
Legacy systems typically refer to outdated computing software, hardware, or technologies that continue to be used despite newer alternatives being available. These systems persist for several compelling reasons.
- First, they often represent significant capital investments that organisations are reluctant to write off.
- Second, they contain years or decades of customisation and business logic that would be costly and risky to replicate.
- Third, they may integrate with other systems in ways that make replacement extremely complex.
However, the age of these systems creates multiple security challenges. Many runs on unsupported operating systems that no longer receive security patches from vendors. They may use outdated programming languages or frameworks with known vulnerabilities that cannot be easily fixed. Their architecture often predates modern security principles like defence-in-depth or zero-trust networking. Perhaps most critically, the expertise needed to maintain and secure these systems is becoming increasingly scarce as the professionals who built them retire.
The Business Continuity Imperative
Business continuity depends on the reliable operation of critical systems. When legacy systems are compromised, the impact extends far beyond immediate data loss or system downtime. Ransomware attacks targeting legacy systems have become increasingly common, as attackers recognize these systems often lack modern security defences and represent critical operational dependencies that organisations cannot afford to lose. Operations can grind to a halt, customer trust evaporates, regulatory penalties accumulate, and competitive advantages disappear. Recent high-profile breaches have demonstrated how quickly decades of reputation-building can unravel when security fails.
The financial sector provides a stark example. Many banks still rely on mainframe systems running COBOL code written in the 1970s and 1980s. These systems process millions of transactions daily with remarkable reliability. Yet they were designed when threats came primarily from insiders rather than sophisticated external actors. A breach of such systems could undermine confidence in the entire financial institution, triggering bank runs and systemic risks.
Healthcare organisations face similar challenges with legacy medical devices and patient record systems. These systems contain highly sensitive personal health information protected by strict regulations. A security breach not only violates patient privacy but can also disrupt critical care delivery, literally putting lives at risk.
Strategic Approaches to Legacy System Security
Securing legacy systems requires a multi-layered strategy that balances pragmatism with rigor. Organisations must accept that perfect security is unattainable, but that meaningful risk reduction is both possible and essential.
Network Segmentation and Isolation
One of the most effective protective measures involves isolating legacy systems from broader networks. By creating dedicated network segments with strict access controls, organisations can limit the potential blast radius of any security incident. This approach recognises that if a legacy system cannot be hardened to modern standards, it must at least be contained.
Implementing proper network segmentation means carefully mapping data flows to understand which systems need to communicate with legacy platforms. Air-gapping, where legacy systems are physically disconnected from other networks, represents the extreme version of this approach but may be appropriate for the most critical systems. More commonly, organisations use firewalls, VLANs, and access control lists to create logical boundaries that are monitored and enforced.
Compensating Controls and Defence in Depth
When direct security improvements to legacy systems are impractical, compensating controls become essential. These are security measures implemented around vulnerable systems to reduce risk. Examples include:
- Enhanced monitoring and logging,
- Intrusion detection systems specifically tuned to legacy system behaviour patterns, and
- Strict authentication requirements for anyone accessing these systems.
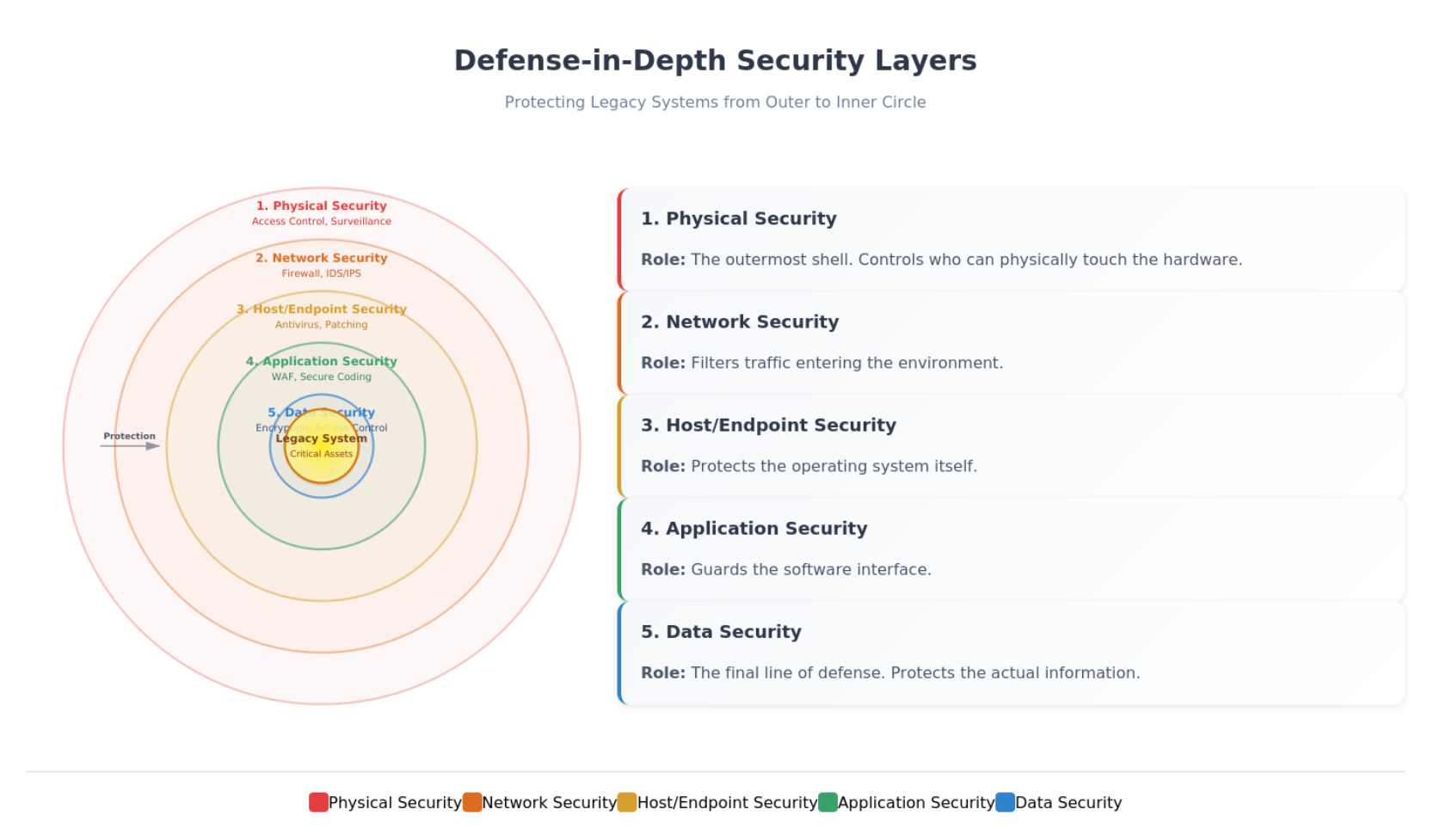
Defence in depth means creating multiple layers of security so that if one control fails, others remain in place. For legacy systems, this might include implementing modern security tools at the network perimeter, deploying endpoint detection and response solutions on systems that interact with legacy platforms, and establishing robust backup and recovery procedures.
Privileged Access Management
Legacy systems often have weak authentication mechanisms and poor audit trails. Implementing privileged access management solutions can address these weaknesses by adding an additional security layer. These solutions control, monitor, and audit all privileged access to critical systems, creating detailed logs of who accessed what and when.
For legacy systems, this might involve implementing jump servers or bastion hosts that act as secure gateways. All administrative access passes through these hardened systems, where it can be monitored and recorded. Multi-factor authentication can be required at this gateway level even if the legacy system itself doesn’t support it.
Virtual Patching and Application Firewalls
When traditional security patches aren’t available for legacy systems, virtual patching offers an alternative. This involves deploying security controls that protect known vulnerabilities at the network layer rather than on the vulnerable system itself. Web application firewalls and intrusion prevention systems can block exploit attempts targeting known vulnerabilities in legacy applications.
This approach requires deep understanding of the vulnerabilities present in legacy systems and the attack patterns that might exploit them. Security teams must create rules that block malicious traffic while allowing legitimate business operations to continue unimpeded.
Modernisation Pathways
While securing legacy systems in place is necessary, organisations should simultaneously plan for eventual modernisation. This doesn’t necessarily mean wholesale replacement but rather a thoughtful evolution toward more secure and maintainable architectures.
Encapsulation and API Layers
One modernisation approach involves wrapping legacy systems with modern API layers. This creates a clean interface between old and new systems while hiding the complexity and vulnerabilities of the legacy platform. The API layer can enforce modern security standards including strong authentication, encryption, and input validation, even if the underlying legacy system lacks these capabilities.
This encapsulation approach also provides flexibility for future changes. As business needs evolve, modifications can often be made to the API layer without touching the fragile legacy core. Eventually, the legacy system can be replaced entirely while maintaining the same API interface, minimising disruption to dependent systems.
Phased Migration Strategies
Rather than attempting a risky big-bang replacement, successful modernisation typically follows a phased approach. Organisations identify discrete components or functions that can be migrated incrementally. This reduces risk, allows for learning and adjustment along the way, and maintains business continuity throughout the transition.
During migration, both old and new systems often run in parallel, with data synchronised between them. This provides fallback options if problems emerge and allows thorough testing before committing fully to new platforms. However, this parallel operation phase must be carefully managed from a security perspective, as maintaining consistency and controlling access across multiple systems introduces its own challenges.
Building a Security Culture
Technology solutions alone cannot secure legacy systems. Organisations need a culture that prioritises security and understands the unique risks these systems present. This starts with executive leadership acknowledging the problem and committing resources to address it.
Security Training and Awareness
Security awareness training should include specific guidance on legacy systems. Employees need to understand why certain systems require special handling and what behaviours might inadvertently introduce risk. This is particularly important for social engineering defences, as attackers often target the human element rather than technical vulnerabilities.
Preserving Legacy System Expertise
Organisations should also invest in developing or acquiring expertise in legacy technologies. As the professionals who built and maintained these systems retire, knowledge transfer becomes critical. Documenting system architectures, dependencies, and quirks helps preserve institutional knowledge. Mentorship programs that pair experienced veterans with younger professionals can help bridge the expertise gap.
Compliance and Risk Management
Many industries face strict regulatory requirements around security and data protection. Legacy systems often complicate compliance efforts because they lack native security features required by modern standards. Organisations must carefully document how compensating controls and other measures address regulatory requirements even when legacy systems cannot directly comply.
Risk Assessment Frameworks
Risk management frameworks provide structured approaches to identifying, assessing, and mitigating security risks. Legacy systems should be explicitly addressed in these frameworks, with honest assessments of their vulnerabilities and the potential business impact if they were compromised. This risk-based approach helps prioritise security investments and justify modernisation projects to executives and boards.
Security Testing Validation
Regular security assessments, including penetration testing and vulnerability scanning, help identify emerging risks before attackers exploit them. For legacy systems, these assessments require special care and expertise to avoid disrupting critical operations. However, organisations that skip assessments out of fear of disruption are essentially operating blind to their true security posture.
Incident Response and Recovery Planning
Despite best efforts, security incidents will occur. Having well-developed incident response and disaster recovery plans specific to legacy systems is essential for maintaining business continuity. These plans should account for the unique challenges these systems present, including limited diagnostic capabilities, scarce expertise, and complex dependencies.
Developing Incident Response Procedures
Incident response procedures should clearly define roles and responsibilities, communication protocols, and escalation paths. Teams need regular training and tabletop exercises that specifically include legacy system compromise scenarios. This preparation ensures faster, more effective responses when actual incidents occur.
Recovery and Restoration Planning
Recovery planning must address both technical restoration and business continuity. How long can operations continue if a legacy system is unavailable? What manual workarounds exist? Where are the most recent backups, and how long does restoration take? These questions should have clear answers before an incident occurs, not during the chaos of a crisis.
Conclusion
Securing legacy systems represents one of the most challenging aspects of modern cybersecurity. These systems cannot simply be ignored or wished away; they will continue supporting critical business functions for years to come. However, organisations that treat legacy systems as unchangeable facts of life rather than manageable risks set themselves up for catastrophic failure.
The path forward requires both pragmatism and commitment. In the short term, organisations must implement comprehensive security measures around existing legacy systems, accepting that perfect security is impossible, but meaningful risk reduction is achievable. Simultaneously, they must plan and execute thoughtful modernisation strategies that gradually reduce dependence on vulnerable platforms.
Success requires investment in both technology and people. Security tools, compensating controls, and monitoring systems provide the technical foundation. But equally important are the expertise, processes, and culture that ensure these tools are used effectively. Organisations that view legacy system security as a strategic priority rather than a technical nuisance will be better positioned to maintain business continuity and customer trust in an increasingly dangerous digital environment.
The cost of securing legacy systems varies depending on the age and architecture of the systems involved. While truly obsolete systems may require substantial investment in compensating controls and workarounds, many legacy systems are simply older technologies that can be secured through standard practices like applying available patches, implementing proper access controls, and enhancing monitoring capabilities. The key is to conduct a thorough assessment of each system to determine the most cost-effective security approach. However, regardless of the investment required, the cost of failing to secure these systems can be far greater. In an era where data breaches make headlines regularly and regulatory penalties reach into the billions of dollars; organisations cannot afford to leave their legacy system as undefended weak points. The question is not whether to secure these systems, but how to do so most effectively and efficiently while planning for their eventual modernisation.